SEO-Enhanced Attacks and Malvertising
Table of Contents
SEO-amplified attacks
What is SEO?
SEO stands for “Search Engine Optimization” and aims to optimize a website or a web page to improve its visibility and placement in search engines’ organic search results. The goal of SEO is to increase traffic to the website by improving its visibility of relevant search terms and thus attracting more visitors.
What is an SEO Attack?
Hackers use SEO in the same way that companies use search engine optimization (SEO) to increase the rankings of certain terms to promote their products and drive traffic to a website.
This is done to boost the ranking of a malware website to send more victims in their path. Today, companies have become much better at blocking incoming attacks such as phishing or smishing through various types of security checks. Therefore, hackers are trying to trick users using novel techniques like the so-called watering hole attack, by making use of SEO.
Hackers can be seen using the same keywords as a regular company to get the malicious variant of a product or blog at the top of these search results. The Gootloader attack is one example. Using users who searched for “legal agreements”, hackers increased their ranking on this particular keyword to trick a user into downloading a free version of a legal agreement template.
Malvertising
What is SEM?
SEM stands for “Search Engine Marketing” and includes marketing strategies and techniques to promote a website through paid ads in search engine results. Unlike SEO, which focuses on improving organic search results, SEM is all about buying ad space and placing ads that appear when users search for specific search terms.
So, what is Malvertising?
Malvertising is a technique where hackers use SEM to promote digital ads injected with malicious code. Since SEM is closely related to SEO, Malvertising, and SEO attacks are usually used in combination with each other.
Hackers have found using paid search techniques for user-targeted ads to be advantageous in carrying out attacks and in fact, malvertising has recently been added as a new technology in MITRE ATT&CK. (https://attack.mitre.org/techniques/T1583/008/) These are most often used in connection with a so-called Drive-By attack where you use JavaScript to attack a user’s browser.
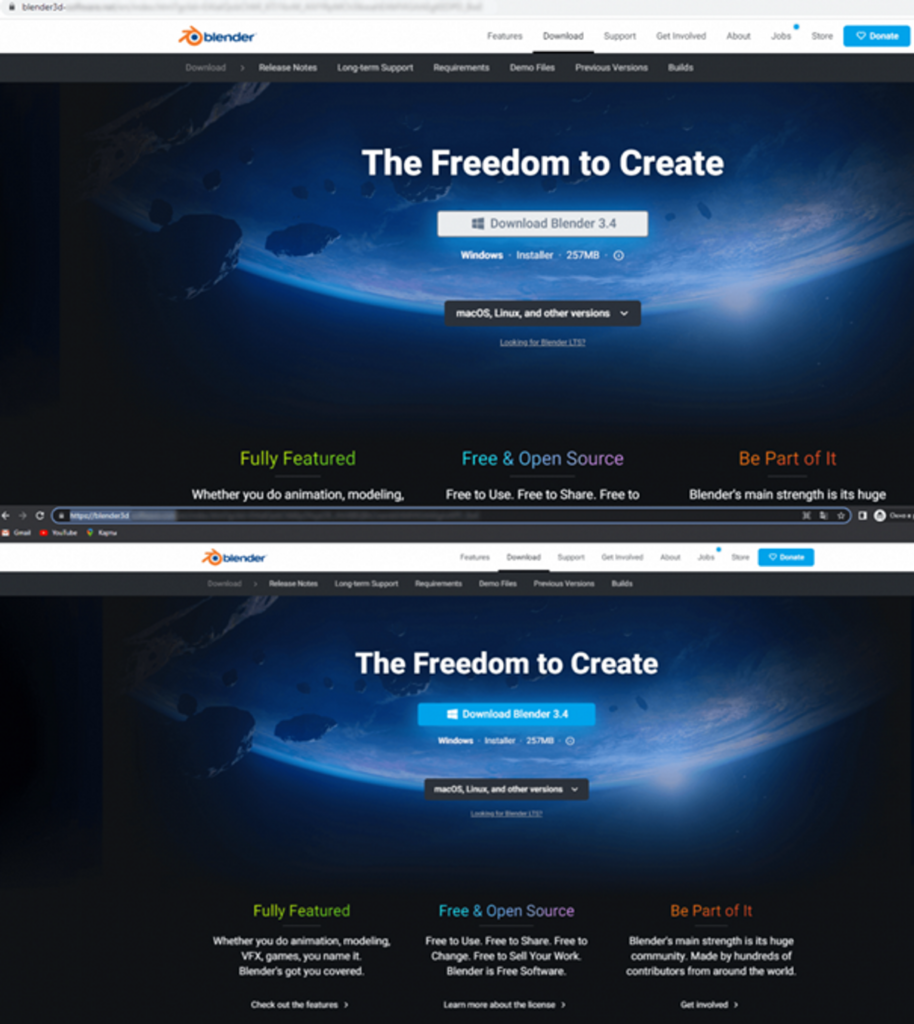
A recent example was when a campaign was launched for the popular 3D graphics software Blender, where one could search for this and the first 3 ads that appeared were malicious malware. It was only the 4th ad that was legitimate. What makes it worse is that the landing pages are so good that it looks like it comes from the company in question. Shown below are examples of such fake pages:
What can we do?
Although none of these technologies are new, we see that these attacks are increasing as we get better and better at having internal security controls. Hackers are trying to find new ways to exploit users. Therefore, users must be educated and made aware of these types of attacks in order to secure systems from cybercriminals. We have initiated this with our recently launched product, Complorer Security Awareness Training.
References
- https://www.csoonline.com/article/575193/5-most-dangerous-new-attack-techniques.html
- https://attack.mitre.org/techniques/T1608/004/
- https://securelist.com/malvertising-through-search-engines/108996/
This post is also available in:
Svenska