Vulnerability Scanning Service
Application vulnerability scanning is a regular security health check and a recommended action in a continuous vulnerability management process.
About eBuilder Vulnerability Scanning Service
Having a vulnerability management program and application scanning, if you have your own application, is ranked high in what is called basic cyber hygiene since it is an important part of the detection phase of any cyber security framework that is implemented. With eBuilder Vulnerability Scanning Service, relish a number of benefits such as:
- Low Monthly Cost
- Not bound with Licenses
- No internal team required
- Data in Sweden – Private Cloud
- On tap – Easily Scalable
- High Detection & Accuracy
Staying Ahead
Cybercrimes are skyrocketing. AIG predicts the annual damages for cybercrimes to reach 10.5 trillion dollars by 2025, which is almost half the US GDP. Cybercrimes have become an industry with traditional products and services. Hacking tools can be rented or purchased as regular software.
The level of sophistication is growing each year. Preventing a cyber-attack is essential to stay ahead of a growing threat to organizations across the world.

If our Tool Finds a Vulnerability, Take Immediate Action Before Someone Else Does.
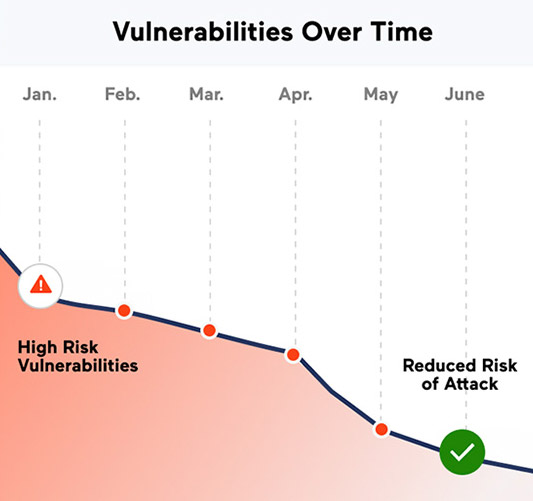
Our service can detect vulnerabilities early on compared to a penetration test which is a less frequent and lengthy process. A vulnerability scan can take anything from a few minutes to a few hours depending on the size and complexity of the application. It can also be conducted at a fraction of the cost of a penetration test and can be run daily or weekly. Hence if a new vulnerability is present, it will be automatically detected faster than in any other detection mechanism.
Benefits of eBuilder Vulnerability Scanning Services
With eBuilder vulnerability scanning services, you can enjoy key benefits such as:
- Quick and easy deployment of services
- Clear reports of vulnerabilities discovered
- Actionable and prioritized recommendation guidance
- Help and guidance regarding future security investments and automated processes
- Control over your cyber hygiene to avoid giving hackers an easy way to compromise your organization
What should be included in a vulnerability scan report?
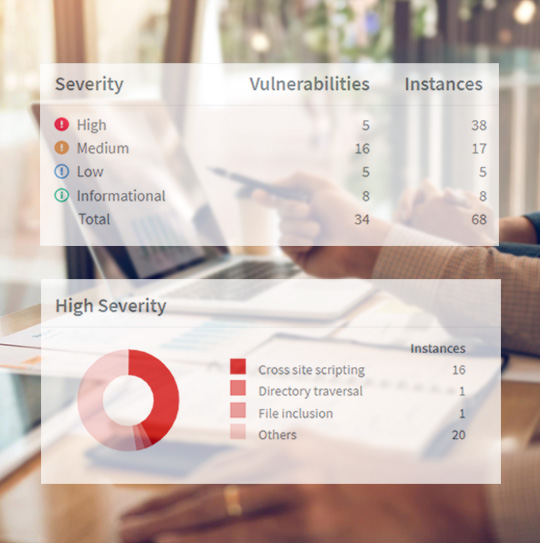
The final step in vulnerability scanning, providing a report with the analysis, should include the following several key items:
- An Executive Summary – Summary of all the vulnerabilities discovered during the analysis categorized by their severity.
- Risk and Impact Analysis – Detailed analysis of the discovered vulnerabilities and their implications.
- Recommendation – Our recommendation on how to mitigate each vulnerability.
Need Help? We’ve Got Your Back.
eBuilder can help you scan the system and deliver the report with remediation actions and are there to guide you through the process. We can, if requested, retest the discovered vulnerability to make sure it has been mitigated or removed.
What Our Clients Say
“Cybersecurity has top priority in our firm. Our software is installed on Exchanges and Central Depositories around the World. We chose eBuilder Security because of their extended experience in delivering secure SaaS to global organizations.
We are very happy with their professionalism and customer service.”
Frequently Asked Questions
Why should I do this?
Comparatively, penetration testing is more expensive. A scan is able to provide an accurate indication of the vulnerabilities of your site regularly, either monthly or at every new release, and is much quicker than a penetration test.
How long does it take?
It can take anything from a few minutes to a couple of hours depending on the size of the site.
How often should I do it?
For a changing site or a business-critical site, we recommend scanning every month and/or when there are major changes. For a site that is more static every quarter could suffice.

Let us show you how we can help your organization
For starters, we can show how to improve upon your existing security in 30 mins. Care to proceed?

