Automated Network Penetration Testing
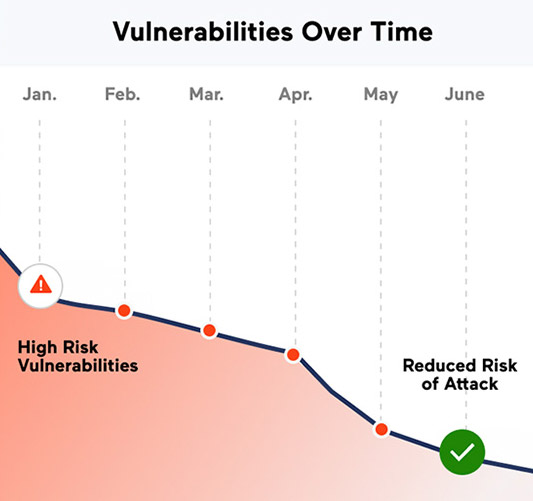
Let us try and attack you, so we can find and fix your vulnerabilities before a cybercriminal exploits them.
About Automated Network Penetration Testing
Automated network penetration testing is a platform that combines the knowledge, methodology, processes, and toolsets of a team of security consultants into a single platform for easy use and access.
We help organizations perform penetration tests within their environment at any given time, satisfying both compliance requirements and meeting network security best practices. This platform is automated and is based on a framework that continuously improves over time.
Why Use eBuilder Security?
By having the ability to perform a quality network penetration test whenever you want and however often you want, your organization can be assured that it will continuously meet security best practices and compliance regulations. Additionally:
- No more scheduling conflicts.
- A full-blown penetration test, whenever you need, however often you need.
- Developed a framework and methodology that changes and improves as the industry threats increase.
- Backed by 10+ years of experience and OSCP, CISSP, CEH, and OSCE certified consultants.
eBuilder Network Pentest Methodology
eBuilder Security platform combines multiple methodologies that were once manually conducted into an automated fashion to consistently provide maximum value to organizations.
The service will include the following:
- Automatic egress filtering to ensure that your organization is effectively restricting unnecessary outbound traffic.
- Automatic validation of user account credentials which is a common process executed by both malicious attackers and penetration testers.
- Identification of crucial areas within your organization using a valid set of credentials. This is conducted through a variety of methods, including our Leprechaun tool.
- We help protect your critical data by simulating and logging activities where confidential or sensitive data can be accessed
- With elevated access, we will attempt to upload malicious code into remote systems to test the organization’s end-point anti-malware controls.
What should be included in a network pen test report?
The final step in network pen testing, providing a report with the results of the analysis, should include the following several key items:
- An Executive Summary – Summary of all the risks discovered during the assessment categorized by their severity.
- Risk and Impact Analysis – Detailed analysis of the discovered risks and their implications.
- Recommendation – Our recommendation on how to mitigate each risk.
Reports will be available within 48 hours (about 2 days) of a test. Our detailed deliverables will allow your staff to cross-reference our activities with monitoring and alerting controls.
What Our Clients Say
“Cybersecurity has top priority in our firm. Our software is installed on Exchanges and Central Depositories around the World. We chose eBuilder Security because of their extended experience in delivering secure SaaS to global organizations.
We are very happy with their professionalism and customer service.”
Frequently Asked Questions
Why should I do it?
If an attacker has breached your external defenses, you need to mitigate and make sure you have the least privileged organization to limit the attackers’ reach and what they can do.
How long does it take?
It depends on what you scan but it can take a few minutes to a few hours.
How often should you scan?
We recommend scanning every month or every quarter. It depends on how much your infrastructure changes over time. Example: due to the patching process.
What should you scan?
We recommend scanning every device that is connected to the network. Everything from servers to printers and access points.

Let us show you how we can help your organization
For starters, we can show how to improve upon your existing security in 30 mins. Care to proceed?

