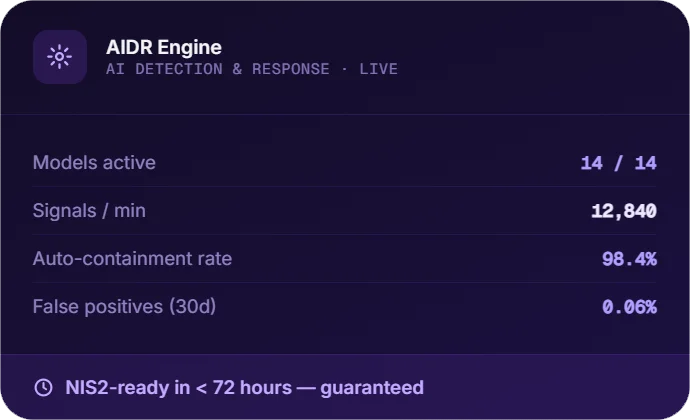
AI Detection & Response
Safe AI adoption for businesses
Monitor prompts, agents, models and sensitive data in real time to reduce AI-driven risk, prevent data exposure and block threats in real time.
We stop attackers before they reach your data with a 3-minute median response, delivered by our Sweden-based SOC and built to support NIS2 and GDPR requirements.

Selected for a strategic, multi-year cybersecurity engagement focused on strengthening resilience and secure digital operations within Sweden’s critical public sector environment.
Trusted by 30+ Swedish Kommuner, Regions and
EU-regulated Enterprises Since 2003







Five specialised cybersecurity services built to strengthen your organisation from real-time threat response to employee awareness.
Safe AI adoption for businesses
Monitor prompts, agents, models and sensitive data in real time to reduce AI-driven risk, prevent data exposure and block threats in real time.
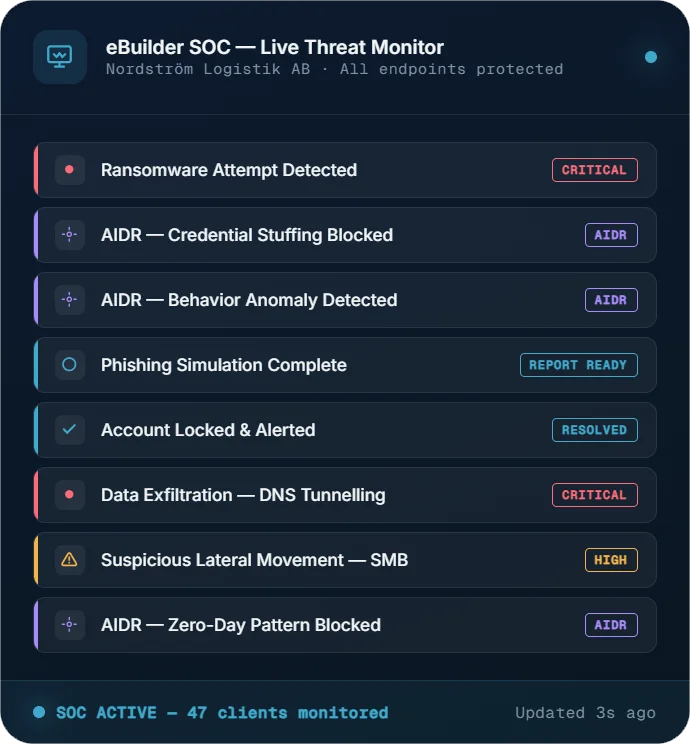
Managed Detection & Response
Our Sweden-based SOC monitors endpoints, identities and cloud workloads 24/7. When threats arise, an analyst responds within three minutes.
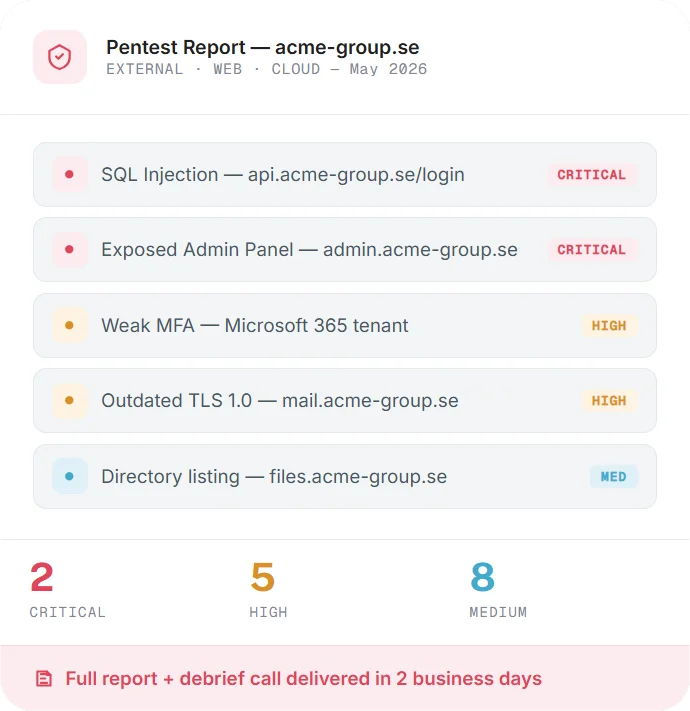
Offensive Security
Expert-led security testing across web, cloud, API, network and Active Directory environments with practical guidance on how to fix what matters.
& Phishing Simulation
Build employee readiness with nano training lessons and realistic phishing simulations that reduce risky behaviour and strengthen your human layer of defence.
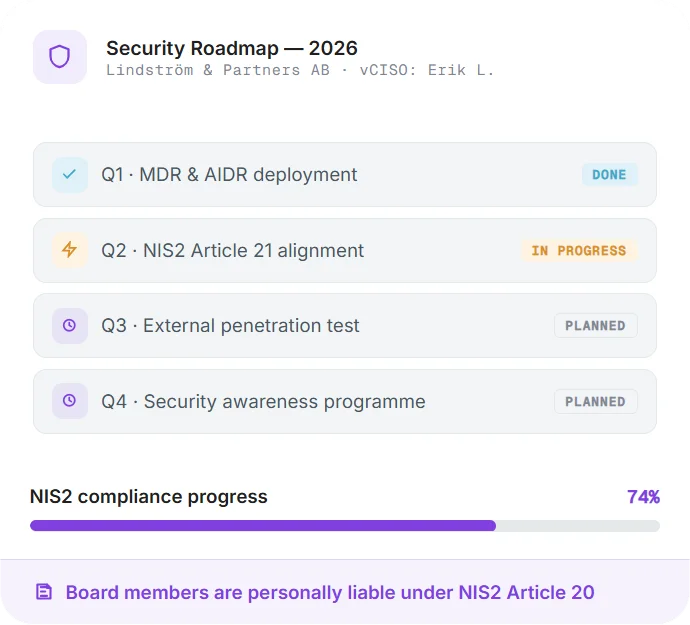
Strategic Advisory
Access senior cybersecurity expertise for governance, compliance, vendor risk and incident readiness without the cost of a full-time CISO.
FREE 30-MIN SECURITY REVIEW
We'll review your current posture and recommend the right mix.
Talk to an ExpertWe are a Swedish security partner focused on transparency, consistency and long-term trust. Our approach is grounded in strong governance, close client relationships and security delivered by people who stay accountable.
Who We AreHuman analysts watching every signal, every minute, every day. Logs stay in Sweden.
The industry talks in hours. We measure in minutes and escalate threats fast enough to matter.
Signed Monday. MDR live Thursday. Complorer rolled out by Wednesday.
Cybersecurity practice within eBuilder, a Swedish enterprise-software company operating since 1999.
Independently audited and certified to the ISO 27001 information-security standard for our SOC.

All services mapped to NIS2 Article 21 risk-management measures.
Human-led monitoring, secure data handling and infrastructure aligned with GDPR and Schrems II requirements.
Explore how each service moves from planning to operation, with clear milestones, defined ownership, and expert support at every step.
A CrowdStrike Falcon or Cybereason sensor is deployed to all endpoints through your existing MDM with no user interruption. We handle the policy configuration and confirm full coverage before moving forward.
AIDR's machine-learning models study what normal looks like in your environment: user patterns, process chains, and network flows. That baseline is what keeps detection sharp and false positives low from the start.
Your environment goes live inside our 24/7 SOC. A named senior analyst is assigned, someone you can reach by name when it matters. Escalation runbooks are written for your organisation specifically, and NIS2 Article 21 controls are documented alongside them.
AIDR contains threats in milliseconds while human analysts validate and escalate within three minutes. Monthly threat intelligence summaries and a quarterly review keep your leadership informed and your posture improving.
We define all targets, agree on methodology (black, grey or white-box), sign an authorisation letter, and confirm the test window. Everything is written down before any testing begins.
CREST-certified testers examine web, network, cloud, API and Active Directory surfaces using a mix of automated tooling and manual techniques. Findings are chained together the same way a real attacker would approach them.
Every finding is documented with its exploitability rating, business impact, and remediation guidance. A live debrief with your team makes sure the results are understood and fixes are tackled in the right order.
Critical and high-severity findings are retested at no additional cost to confirm the fixes hold. The final report is suitable for your board, your auditors, or a regulatory submission.
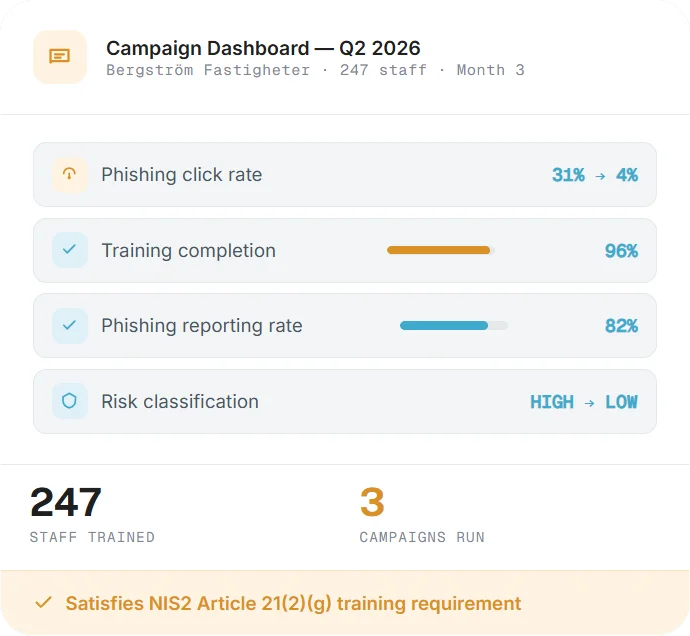
An unannounced phishing campaign measures your current click and report rates across the organisation. It gives you an honest starting point before any training begins, and something concrete to measure against later.
Short, role-based lessons are sent to staff through Complorer, tailored to each person's role and the outcome of the baseline simulation. Content is concise and contextual, and no separate LMS login is required.
Simulation scenarios become progressively more realistic over time, covering spear-phishing, voice pretexting and QR-code lures. The goal is to build genuine vigilance rather than create compliance fatigue.
Click-rate trends, the most targeted roles, and improvement over time are delivered in a management-ready report. NIS2 Article 13 awareness-training documentation is included with every quarterly summary.
We review your current controls, gaps, vendors and risk register against ISO 27001 and NIS2 requirements. You leave with a prioritised list of actions, not a lengthy presentation.
Policies, procedures and risk treatment plans are written to your specific regulatory context, whether that is NIS2, ISO 27001, GDPR or sector requirements. Everything is editable and owned entirely by you.
Third-party risks are mapped, scored and addressed through updated contracts, questionnaires and compensating controls. NIS2 Article 21(d) supply-chain obligations are documented in a way that holds up to scrutiny.
Monthly sessions, tabletop exercises and on-call escalation support keep your leadership aligned and your team ready. You get the clarity of a senior security leader without the overhead of a full-time hire.
2m 47s
Mean Time to Contain
A Swedish municipality was targeted after hours. Our SOC picked up anomalous lateral movement, isolated the infected host and notified the CTO within 2 minutes 47 seconds. No data was lost.
72hrs
NIS2 Compliant from Zero
A 400-employee manufacturer with no dedicated security function needed Article 21 documentation in place before a regulatory audit. We assessed, deployed and documented in 68 hours, completing two days ahead of schedule.
94%
Training Completion Rate
A Swedish retail group needed to demonstrate NIS2-aligned security awareness across its full workforce in four weeks. Complorer delivered role-based training to 3,200 employees, reaching 94% completion. The audit passed with zero findings.
14days
Time to Close All Criticals
An internal penetration test of a Swedish insurance firm uncovered a full domain takeover path through unconstrained Kerberos delegation. All critical and high findings were remediated and confirmed clean on retest within 14 days.
4yrs
Zero Breaches Under Coverage
A Swedish logistics operator running 14 sites has been under 24/7 MDR coverage with a named analyst team for four years. No successful breaches. Full NIS2 Article 21 compliance documentation has been maintained throughout the engagement.
Sweden's Cybersäkerhetslagen brought NIS2 into national law. If your organisation operates in energy, transport, health, digital infrastructure or public administration, you are in scope. Here is what Article 21 requires in practice.
Our NIS2 gap checklist maps your current state against every Article 21 control. It is written in plain English, built for the Swedish regulatory context and takes around 20 minutes to complete.
See where you stand on Articles 20 and 21, scored in plain language. The output is board-ready and reflects current MSB guidance.
No spam. EU data residency. Unsubscribe any time.
eBuilder Security helps us meet our IT and information security needs. We are very satisfied by their deep knowledge, comprehensive services, and dedication to strengthening our cybersecurity posture. From End Point Protection and advisory and auditing to penetration testing, eBuilder Security has been a reliable partner in safeguarding our organization.

Christian Sørensen
Internal Operations Director, Médecins Sans Frontières, Norway
The product increases knowledge and security awareness. It helps organizations develop a good information security culture. I am particularly pleased that it is an end-to-end solution where eBuilder Security takes care of the entire process from kick-off to reporting, while allowing for customization to suit the conditions unique to our business.
Per Eriksson
Information Security Strategist, Varbergs Kommun, Sweden
Through their range of security services and our decision to choose their MDR solution, eBuilder Security has significantly elevated our security posture. During the implementation phase, they were quick to assist and propose solutions to any challenges we encountered. The transition from project to production has been smooth, and their backend team quickly grasped our business needs. eBuilder Security is a valued partner for our future security efforts.
Gerth Ericsson
IT Manager, Vandewiele, Sweden
Book a 30-minute walkthrough with a Sweden-based analyst. We'll review your current posture, map gaps to NIS2 and show you live SOC in action.
Book a 30-Minute Security Briefing